Part II: Signal Monitoring Techniques
October 2023In the previous issue, we introduced the practice of signal monitoring, as well as enumerated some of its main objectives. In this issue, we introduce popular signal monitoring techniques.
Signal monitoring techniques are methods used to observe, analyze, and interpret various types of signals, such as electronic, electromagnetic, or digital signals.
These techniques are used in a wide range of fields, including telecommunications, electronics, cybersecurity, and more.
1. Spectrum analysis, which is commonly used in radio frequency (RF) and wireless communication systems, involves examining the frequency components of a signal to understand its frequency distribution, bandwidth, and any potential interference.
2. Time-Domain analysis involves studying the signal’s behavior over time, looking at parameters like amplitude, frequency, and phase variations. It’s often used for analyzing transient signals or signals with changing characteristics.

3. Power monitoring measures the power level of a signal, which is crucial for maintaining proper signal integrity and avoiding overloads (when the voltage of an incoming signal is higher than the voltage range the sensor or data acquisition system can handle) or distortions in electronic circuits.
4. Protocol analysis involves monitoring the exchange of data packets (small units of information transmitted over a network), messages, or commands between devices to ensure proper communication and detect any errors or anomalies.
5. Network Traffic analysis involves to monitoring network traffic patterns, identifying potential security threats, abnormal behaviors, or performance issues.
6. Deep Packet Inspection (DPI) involves inspecting the content of data packets in a network to gain insights into the type of traffic, applications being used, and potential security risks.
7. Wiretapping and eavesdropping techniques involve intercepting and monitoring electronic communications to gather information. While this can be used for legitimate law enforcement purposes, it can also raise serious privacy and ethical concerns.
8. Radio Frequency Identification (RFID) monitoring systems use radio waves to identify and track objects. Monitoring RFID signals can help with inventory management, asset tracking, and access control.
9. Digital Signal Processing (DSP) techniques are used to process and analyze digital signals, such as audio, image, and video signals. These methods involve operations like filtering, modulation, and noise reduction.

10. Anomaly detection techniques identify deviations from normal signal behavior, which can be used for various applications such as intrusion detection, fault diagnosis, and fraud detection.
11. Audio and video monitoring, as the phrase suggests, is important for industries such as broadcasting, surveillance, and multimedia content creation.
12. Packet sniffing involves capturing and analyzing data packets on a network to understand the flow of information, troubleshoot issues, or monitor network activity.
13. Environmental signal monitoring includes techniques like seismic monitoring, weather radar, and pollution sensing, which are used to monitor natural phenomena and environmental conditions.
14. Cybersecurity monitoring employs techniques like intrusion detection systems (IDS) and intrusion prevention systems (IPS) are to monitor network traffic and identify potential threats or attacks.
These techniques play a crucial role in understanding, optimizing, and securing various types of signals and communication systems. Most importantly, some monitoring activities, especially those involving privacy-sensitive data, must be conducted in accordance with legal and ethical guidelines.
Latest Posts
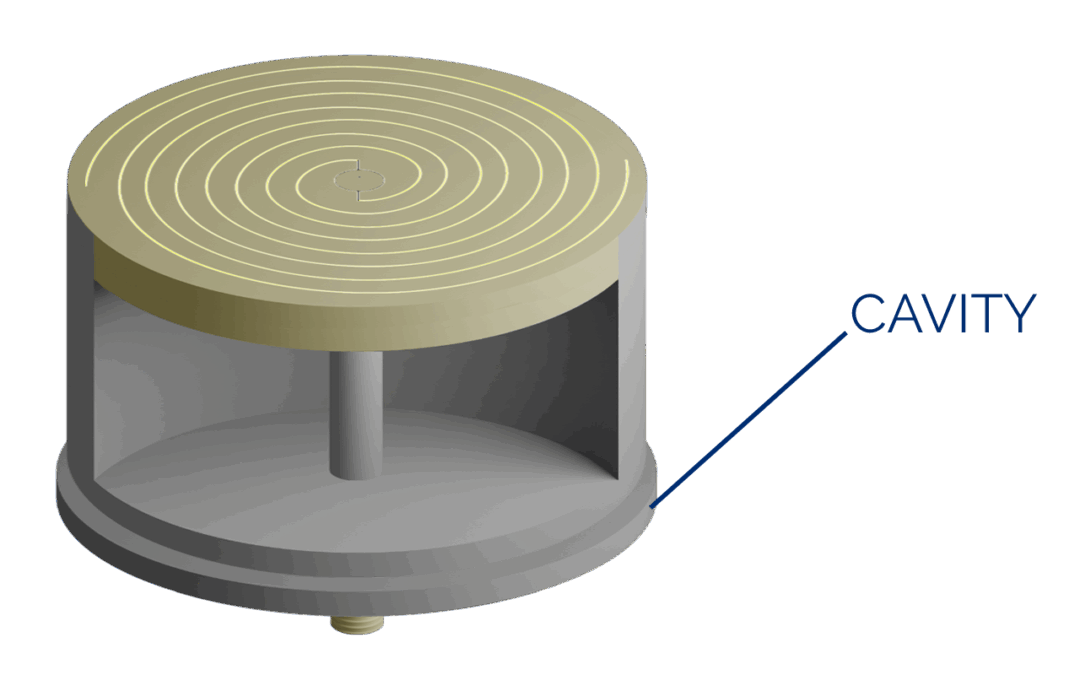
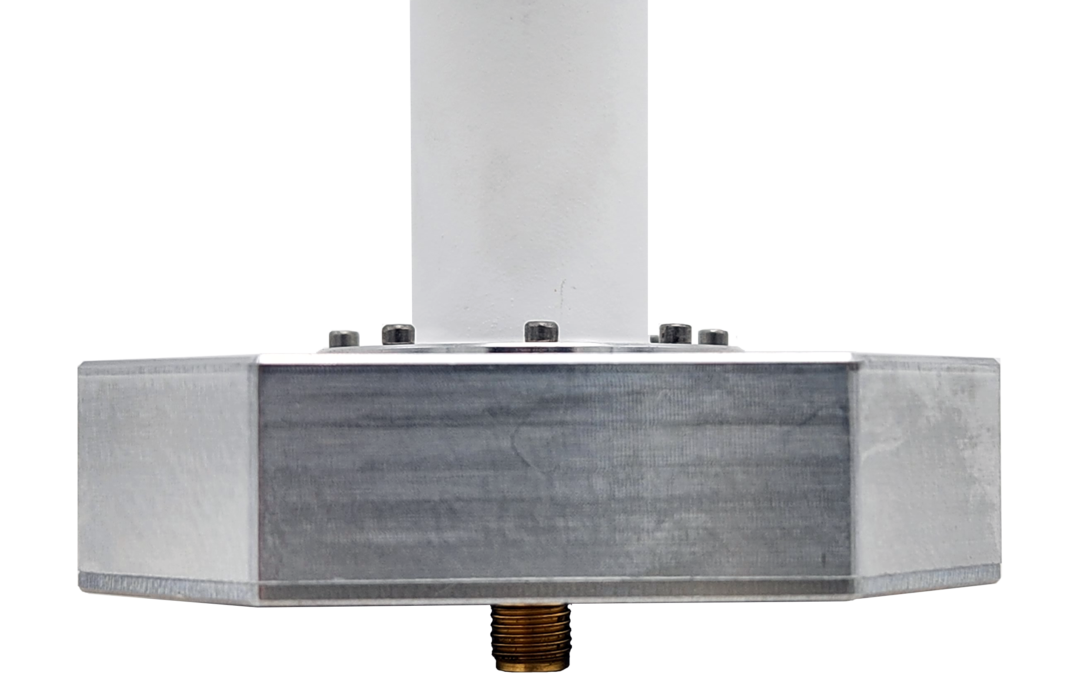
Spiral Series: The Cavity-Backed Spiral
Spirals are considered frequency-independent antennas, mostly because their characteristics like polarization, radiation pattern, and impedance remain relatively constant over a broad range of frequencies.

An Abundance of Aircraft Antennas
Home » Media Center » Blog » An Abundance of Aircraft AntennasWhen you look at an aircraft, you...
Which Antennas are Suitable for Sensor Systems?
Sensor antennas play a crucial role in various applications, including environmental monitoring, wireless sensor networks (WSNs), IoT devices, and industrial automation, medical devices, radar and navigation. These antennas come in different types, each designed for specific sensor systems and frequency ranges.
